The aggressive escalation of regulatory oversight on both sides of the Atlantic has fundamentally transformed the digital landscape, with multimillion-euro GDPR penalties for tracking pixels and stern HIPAA warnings regarding routine analytics becoming common occurrences. This environment has created an unprecedented “compliance squeeze” for Chief Information Security Officers and privacy professionals who are now tasked with navigating a labyrinth of overlapping international mandates. The shift toward compliance automation represents a pivotal transition from manual, spreadsheet-based record-keeping to a dynamic, technology-led approach that seeks to provide continuous oversight rather than static, point-in-time snapshots of organizational health.
Modern regulatory technology operates on the principle that the velocity of data flow in a cloud-native world has surpassed the capacity of human auditors to track it manually. Historically, achieving certification for frameworks like SOC 2 or HIPAA required months of painstaking evidence collection, resulting in a stack of documentation that was often obsolete the moment it was signed. Current software solutions disrupt this cycle by utilizing deep API integrations to transform compliance into a persistent, living process that mirrors the real-time nature of the infrastructure it monitors.
Evolution and Context of Compliance Automation
Compliance automation first emerged as a survival mechanism for fast-moving technology startups that found themselves excluded from enterprise contracts due to a lack of formal certifications. These early tools focused primarily on the “security-first” frameworks, providing a way to verify that encryption was active or that employee onboarding followed a set script. However, the scope of these platforms expanded rapidly as global privacy laws, specifically GDPR and the CCPA, introduced stringent requirements for how data must be handled, stored, and deleted across disparate systems.
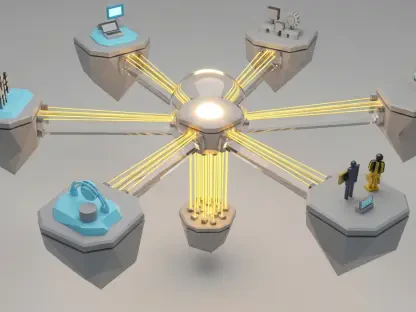
The current generation of these platforms moves beyond simple checklists to offer integrated “PrivacyOps” environments. This evolution was driven by the realization that security controls and privacy requirements are two sides of the same coin; one cannot effectively protect personal identifiable information without the underlying technical safeguards that automation provides. By centralizing these functions, organizations can now manage their global regulatory footprint from a single pane of glass, reducing the administrative burden that once paralyzed internal IT teams and legal departments.
Key Features and Core Components of Compliance Platforms
Continuous Monitoring and Automated Evidence Collection
The hallmark of a high-performing compliance platform is its ability to maintain what is often described as a “breathing” control matrix. By establishing direct connections with an organization’s technology stack—including cloud providers like AWS, identity managers like Okta, and version control systems like GitHub—the software pulls fresh evidence every few minutes. This continuous loop ensures that an organization remains in a state of “audit readiness” at all times, rather than rushing to fix gaps during a frantic end-of-year review cycle.
This level of automation provides a level of granular visibility that was previously impossible to achieve. For instance, if a developer accidentally misconfigures a database bucket to be public, the compliance engine identifies the deviation from the required security policy and flags it instantly. Instead of waiting for an auditor to find the error months later, the system provides a real-time corrective path, thereby significantly reducing the window of vulnerability and the associated risk of a data breach or regulatory fine.
Data Discovery and Intelligent Classification
A critical advancement in these platforms is the implementation of specialized classifiers that provide “x-ray vision” for sensitive data across complex environments. Traditional tools often struggled to differentiate between generic files and those containing protected health information or personal identifiers. Modern compliance engines utilize machine learning models to recognize ICD-10 codes, insurance account numbers, and even free-text diagnoses, automatically tagging these assets with the appropriate regulatory safeguards for HIPAA or GDPR compliance.
This capability is particularly vital for organizations dealing with massive amounts of unstructured data stored in cloud buckets or on-premises servers. By building a comprehensive and automated data inventory, the software allows a company to accurately map its data flows and identify exactly where sensitive information resides. Understanding the geographical and technical location of data is the first step toward satisfying the strict data residency requirements found in modern privacy legislation, ensuring that information does not cross borders without the necessary legal protections.
Automated Workflow Orchestration and Remediation
Beyond the identification of data and controls, modern platforms excel at orchestrating the necessary responses to regulatory events. One of the most resource-intensive tasks for a privacy office is the fulfillment of Data Subject Access Requests, where individuals ask to see or delete their personal information. Advanced automation platforms use intelligent bots to crawl the entire corporate ecosystem, assemble the relevant data packets, and even flag sensitive healthcare data for redaction before the final report is sent to the requester.
Furthermore, when a control fails—such as an unencrypted database or a missing vendor agreement—the platform can automatically trigger a remediation workflow. This might involve creating a ticket in a project management system like Jira or launching a task list for the legal team to address. By bridging the gap between detection and correction, these platforms ensure that security gaps are closed systematically, preventing the administrative “swivel chair” effect where information is lost between different departments and software tools.
Emerging Trends in Regulatory Technology
The industry is currently gravitating toward a fusion of privacy, security, and IT operations, often referred to as a unified data trust model. The latest technological innovations involve the use of AI-driven People Data Graphs, which link individual identities to specific records and consent flags across multiple continents and cloud services. This allows an organization to see a holistic view of a single person’s data footprint, making it significantly easier to manage complex consent requirements and localized data protection rules without manual intervention.
Moreover, there is a growing trend toward “dual-framework mapping,” where the software identifies commonalities between different laws. For example, a single technical control regarding access logs might satisfy both Article 32 of the GDPR and specific HIPAA technical safeguards. By automatically cross-referencing these requirements, platforms allow organizations to “build once and comply many times,” which drastically reduces the redundant work that typically plagues large enterprises operating in multiple jurisdictions.
Real-World Applications and Industry Deployments
In the healthcare sector, large hospital groups and tele-health providers have deployed these tools to streamline their audit cycles while maintaining the highest levels of patient data security. By automating the evidence collection for SOC 2 and HIPAA, these organizations can focus their internal resources on clinical excellence rather than administrative box-ticking. The software acts as a persistent guardian, ensuring that the infrastructure supporting patient care remains compliant even as it scales and evolves.
Data-heavy enterprises in other sectors, such as marketing and telecommunications, utilize these platforms to manage the complexities of digital consent. With the landscape of Atlantic data transfers constantly shifting, having an automated system to manage cookie banners, tracking toggles, and data processing addendums is a strategic advantage. These deployments have shown that companies capable of proving continuous compliance can build higher levels of consumer trust, which translates directly into competitive benefits in an increasingly data-conscious global market.
Challenges and Implementation Obstacles
Despite the clear advantages, the adoption of compliance automation is not without significant hurdles. Many of the most powerful platforms come with a steep learning curve, often requiring dedicated administrators to manage the initial rollout and ongoing configuration. The sophistication of the tools means that they must be tuned specifically to the unique environment of each organization; a “one-size-fits-all” approach often leads to a deluge of alerts that can overwhelm a small security team.
Financial barriers also remain a concern, particularly for smaller organizations and startups facing “sticker shock” from high licensing fees. Furthermore, the reliance on automation can lead to a phenomenon of “false positives,” where the software flags non-sensitive data as a high-priority risk, requiring significant human intervention to triage and tune the system. There are also legal hurdles to consider, as the technical deployment of these tools often sits in “limbo” while legal departments negotiate the necessary Business Associate Agreements and Data Processing Addendums required to handle sensitive information.
Future Outlook and Technological Trajectory
The trajectory of this technology points toward deeper integration and the rise of predictive compliance capabilities. Future platforms are expected to move beyond reporting on the current status to forecasting potential failures before they occur. By analyzing patterns in system configurations and employee behavior, machine learning models will likely provide early warning signs of a compliance drift, allowing organizations to intervene proactively before a regulatory threshold is crossed or a breach occurs.
As privacy laws continue to fragment globally, the role of automation will become even more central to corporate strategy. The long-term impact will be the commoditization of trust, where the ability to provide real-time, verifiable proof of data protection becomes a standard requirement for doing business. Organizations that successfully integrate these automated systems will be better positioned to navigate the complexities of the future, turning compliance from a costly burden into a streamlined engine for operational efficiency and data integrity.
Final Assessment of Compliance Automation Software
The review of current compliance automation technologies indicated that these platforms transitioned from being a premium luxury to an operational necessity for modern enterprises. The investigation revealed that the primary value of the software resided in its ability to replace static spreadsheets with a continuous, AI-driven oversight model that mirrored the speed of cloud infrastructure. Analysts found that while technical complexity and initial costs presented obstacles, the reduction in manual labor and the mitigation of regulatory risk provided a clear return on investment.
The evaluation determined that the most successful implementations occurred when organizations phased their deployment, starting with high-value integrations before expanding to secondary systems. Experts concluded that the software allowed security and legal professionals to move beyond administrative tasks, focusing instead on the core mission of data protection. Ultimately, the transition to automated compliance was judged as a transformative shift that empowered organizations to maintain trust and transparency in an era of unprecedented regulatory scrutiny. In the final analysis, those who adopted these tools were found to be significantly better prepared for the evolving demands of the global digital economy.